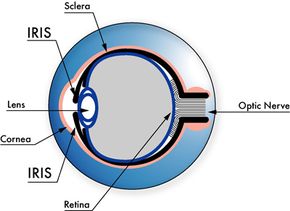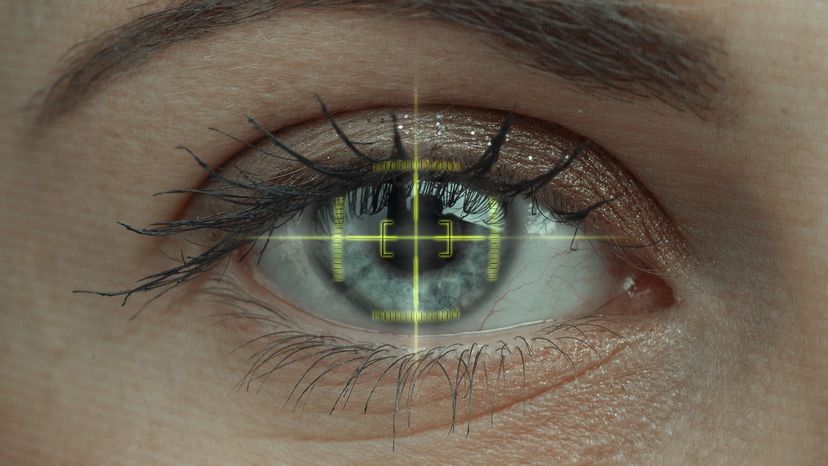
Imagine you're James Bond, and you have to get into a secret laboratory to disarm a deadly biological weapon and save the world. But first, you have to get past the security system. It requires more than just a key or a password -- you need to have the villain's irises, his voice and the shape of his hand to get inside.
You might also encounter this scenario, minus the deadly biological weapon, during an average day on the job. Airports, hospitals, hotels, grocery stores and even Disney theme parks increasingly use biometrics -- technology that identifies you based on your physical or behavioral traits -- for added security.
Advertisement
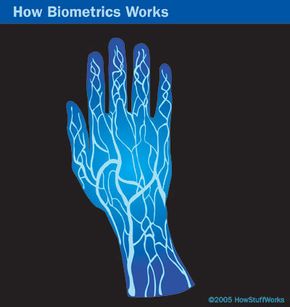
In this article, you'll learn about biometric authentication systems that use handwriting, hand geometry, voiceprints, iris structure, and vein structure. You'll also learn why more businesses and governments use biometric technology, such as facial recognition systems and voice recognition software. Maybe then we'll discover whether Q's fake contact lenses, recorded voice, and silicone hand could really get James Bond into the lab (and let him save the world).